Announcing the Security Partner Program Pack v1
03/31/2025
Introduction
I have built several security partner programs at companies such as Box Inc. and Coinbase, with over 8 years of experience leading them. I have consistently observed the benefits of a partner-focused model versus a classical consultancy model within medium to large enterprises. I'm pleased to announce our 6th program pack, the Security Partners Program Pack. The goal of this program pack is to provide you with minimal information to establish a functioning, and impactful security partner program. This will enable you to adopt a security partnership model, and provide you with a repeatable process to scale up as needed.
- Robert Auger (@robertauger & @sectemplates)
Security Partner Program Release Pack 1.0
A security partner program functions as a white-glove service provided by the security team, offering dedicated support to specific engineering teams. While traditional security operates as a consultancy supporting everyone, a security partner serves as a long-term, dedicated advisor to a specific organization or product line. This approach enables a security engineer to become a subject matter expert on a set of products and their technologies, foster closer collaboration with engineering, and improve communication and understanding of critical changes in product lines. The benefits of the security partnership model include:
- Context - The security partner is aware of past risks in a specific product, familiar with the codebase, core product functionality, and understands current security issues while also anticipating future risks.
- Execution speed - With historical context and familiarity with the product, security reviews such as design reviews and threat modeling can be conducted more efficiently, minimizing delays for the product and engineering teams.
- Advocacy - The security partner understands the challenges faced by the engineering team, including weak security controls in the technologies used, technological constraints, and architectural limitations inherited from shared components and services.
- Trade off identification - As risks are identified, solutions must be researched and proposed to address them. The partner has a comprehensive understanding of the products in their domain and can provide context-specific guidance, enabling quicker decision-making
The goal of this program pack is to provide you with minimal information to establish a functioning, and impactful security partner program. This will enable you to adopt a security partnership model, and provide you with a repeatable process to scale up as needed.
In this pack, we cover:
- ReadMe: Start here first, it instructs you of the order to use the pack and also includes frequently asked questions.
- Definitions: This document defines stakeholders and their responsibilities.
- Preparation checklist: This checklist provides a step-by-step guide to researching, piloting, testing, and rolling out security partners program at your company.
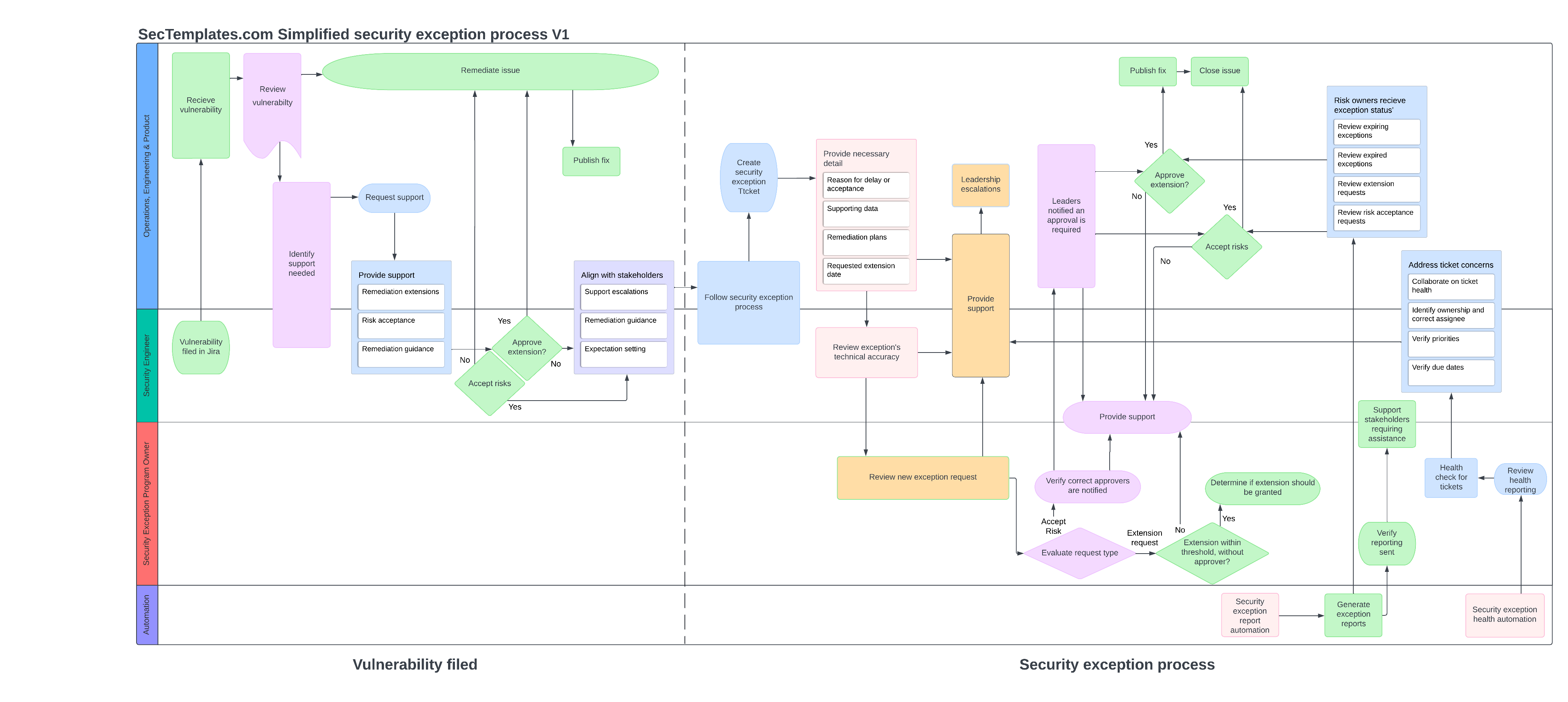
- Process Diagram: This diagram visualizes the various runbooks and activities performed by a security partner.
- Runbooks: This runbook contains the steps outlined in the process diagram as a checklist with a strong focus on stakeholder support.
- Metrics: This document outlines starting metrics for a security partner program. I strongly encourage everyone to experiment with security focused metrics!
GitHub: https://github.com/securitytemplates/sectemplates/tree/main/security-partners
Links
Have an idea for a missing pack? Contact us!
X/"Twitter": https://x.com/Sectemplates
Licensing
This project utilizes a modified creative commons license.
About SecTemplates
To provide simplified, free, and usable open-source templates to enable engineering and smaller security teams to bootstrap security capabilities in their organizations.